Wordpress Attack Protection Authorization Failed! Please Try Again.
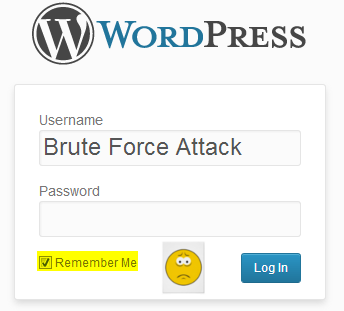
There have now been several large calibration WordPress wp-login.php beast force attacks, coming from a large amount of compromised IP addresses spread across the world since Apr 2013.
We kickoff started this page when a big botnet of around 90,000 compromised servers had been attempting to interruption into WordPress websites by continually trying to guess the username and password to get into the WordPress admin dashboard.
You can rapidly review WordPress login attempts to run into if your site has recently been under attack.
Global WordPress brute force attack
General WordPress brute force protection
Please annotation – before calculation and removing plugins or making changes in general, yous should backup your WordPress with a reputable plugin.
While nosotros do HIGHLY recommend implementing as many secure solutions as possible for WordPress, the following guides would exist a great first footstep in protecting yourself and your WordPress site from farther attacks.
- 10 recommended steps to lock down and secure WordPress (lesser of this guide)
- Setup secondary WordPress admin countersign
- Change WordPress admin URL with iThemes Security plugin
- Limit WordPress admin logins by IP accost
InMotion Hosting's defense programme
Our senior system administration team has rolled out a fleet broad security policy to assist contain these attacks.
Nosotros are proactively protecting our customers to assistance stop the spread of further attacks. These malicious bots are trying to break into one WordPress site, and then using it as function of the botnet to begin attacking other sites.
Helping the community
I took place in an almost 2 hr Google+ hangout with the WordPress Bay Area Foothills Meetup Grouping consisting of some InMotion customers as well every bit other WordPress users.
In this hangout I covered this WordPress fauna strength attack, and walked them through this article likewise as answered other WordPress security related questions.
ten recommended steps to lock downwards and secure WordPress
one. Apply a strong password
Minimum countersign recommendations:
- At least 8 characters total
- Mixture of upper and lower-example letters
- Numbers, punctuation or other non-alphanumeric characters
Example weak password: secret1
Improved strong password: Z#hupsZ2M4!Z
Take a look at how to create a secure WordPress admin countersign for easy steps.
2. Alter default WordPress admin username
When installing WordPress, past default the administrator user has the username of admin.
The botnet assault is currently only targeting this default username, so even having an administrator username of admin123 could significantly reduce the likelihood of your site being successfully logged into by a malicious user.
Check out how to alter the WordPress default admin username for security.
3. Lock downwards WordPress admin access with .htaccess
Utilizing a WordPress brute force plugin for this type of attack is not very efficient, and in some cases can actually lead to your site becoming unavailable due to the big amount of processing power used to endeavour to challenge each and every malicious login attempt.
Setup a secondary level password to prevent unauthorized WordPress wp-admin and wp-login.php attempts.
Or you lot tin can rely on the information nosotros take on limiting WordPress admin access with .htaccess.
4. Temporarily disable CPU intensive login limit plugins
Blocking this attack with .htaccess rules is the preferred method, as login limiting plugins can non simply lead to effect with triggering our own internal security rules, but they besides will non be effective in this type of large scale attack.
5. Scan website for hacks, check Google Safe Browsing
If your WordPress site had been successfully compromised, a clear indication will commonly exist institute either by a surface security scan of the website, or it will besides get reported to Google's Safe Browsing.
Check Google's rubber browsing for your domain, at https://transparencyreport.google.com/safe-browsing/search
6. Setup CloudFlare DNS level protection
Due to the large scale of this botnet assail, CloudFlare has offered DNS level filtering for this assault on all of their free accounts.
While probably not an ideal solution if y'all take many WordPress sites due to having to update the name servers for each domain, and and so waiting typically 24-36 hours for DNS propagation. Single site owners might benefit greatly from this blazon of protection which should block the botnet requests from even making it to the server in the kickoff place.
vii. Fill-in WordPress
At this betoken it'southward probably a skillful thought to backup WordPress merely in case. That way, equally the attacks continue, you're ensured that you always have a practiced indicate to restore back to in the event something goes bad.
Backing upward your information
Restoring your data
8. Update everything WordPress
To protect yourself from any known exploits to WordPress y'all should update everything related to WordPress:
Necessary updates to make:
ix. Clean upwards hacks
If your website has been the victim of a hack, you can follow my guide on how to reinstall WordPress after a hack for steps on cleaning information technology upward and getting back in business.
10. Other general WordPress recommendations
- Optimizing WordPress with W3 Full Cache plugin
- Log out of WordPress admin dashboard when not in employ
- Limit or disable WordPress revisions
- Disable WordPress autosave
- Install and employ Better Delete Revision WordPress plugin
- Become new WordPress Hosting from u.s.a.!
Hopefully your WordPress website should be locked down and secure at present, which should help preclude our own internal security rules from blocking your own access to your WordPress admin.
When the dust settles and you know how to foreclose animal force attacks from getting access, please accept some fourth dimension to review our repository of WordPress Tutorials.
Source: https://www.inmotionhosting.com/support/edu/wordpress/wp-login-brute-force-attack/
0 Response to "Wordpress Attack Protection Authorization Failed! Please Try Again."
Post a Comment